Kerberos Authentication in WAC
Objective
The main objective for this documentation is to finalize a better approach for Kerberos Authentication in WAC project for Domain joined Environment users.
Approach Suggestion
Ticket Reference
AUTHNCLI-904: SPIKE: Document on Approach finalization on FQDN support for domain-join user(s).
RIC-3931: BE: Create BE API for non-domain joined Kerberos Authentication.
Currently RI Admin assigned Authentication Method to user on RI and accordingly WAC display all authentication method list for a user to choose But In WAC we will allow all user(s) to use Kerberos using any supported WAC Authentication Method for domain joined environment so Admin have not need to assigned Kerberos on RI in order to use it .WAC will provides Kerberos for all user(s).
The reason Behind this:
RI allows Admin to Configure Kerberos only for single Service Principle Account’s users at a time.
Any BE API can not connect with AD directly so WAC independently needs to connect with AD validate domain and user(s) credentials and provides FQDN support to user in that case wac will not get any user configuration from RI.(Discussed Earlier)
It will be better if all user can get FQDN support and can login using Email and Short Name (sAmAccountName)
Kerberos Domain-join Authentication Work Flow Diagram:
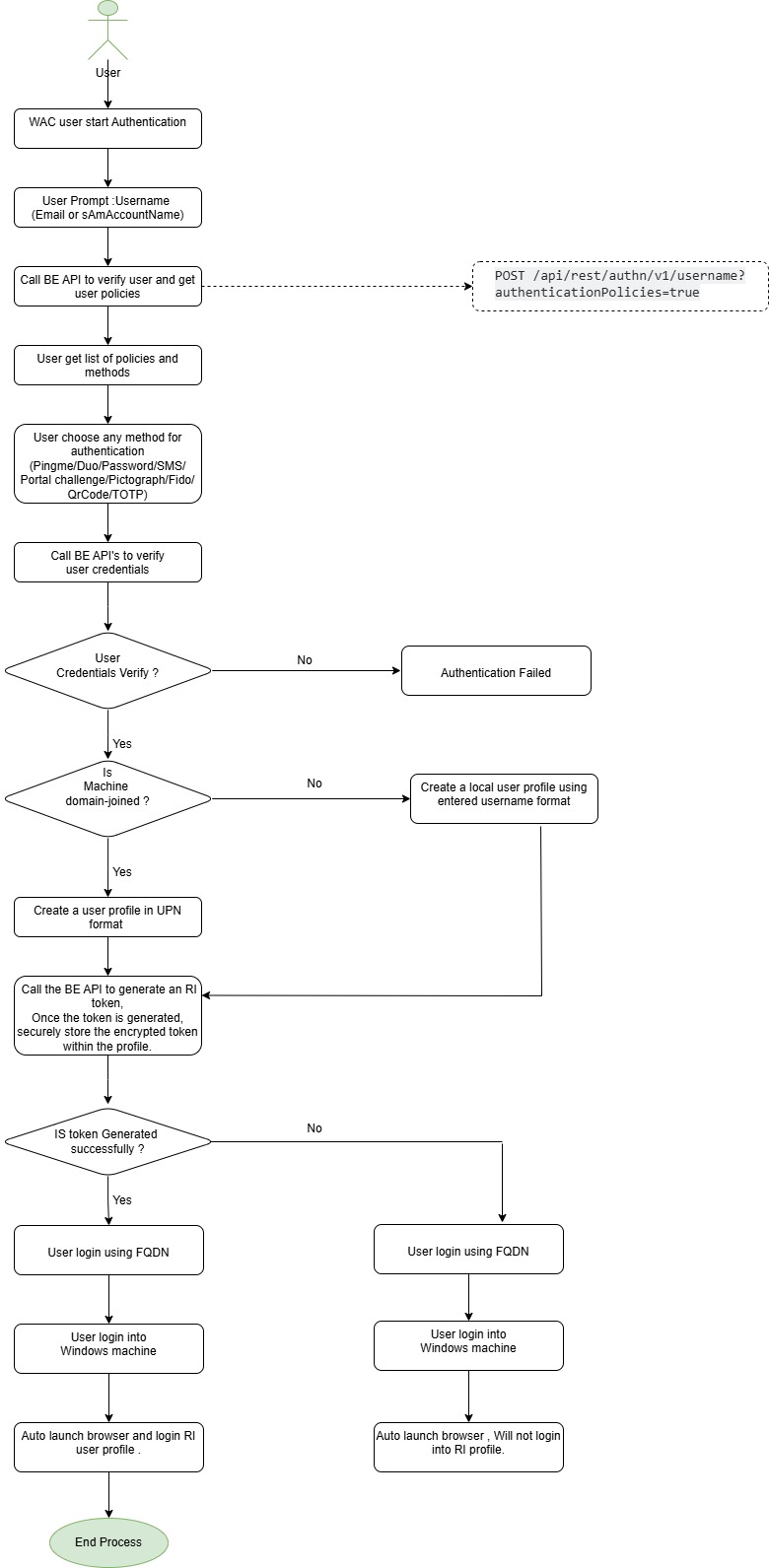
(Mock)Steps for User login process after Kerberos Authentication:
In a domain joined environment Portal launcher will create a single name(UPN) file for all authentication methods to store token.
Step 1: User start login process using Email (UPN) in WAC
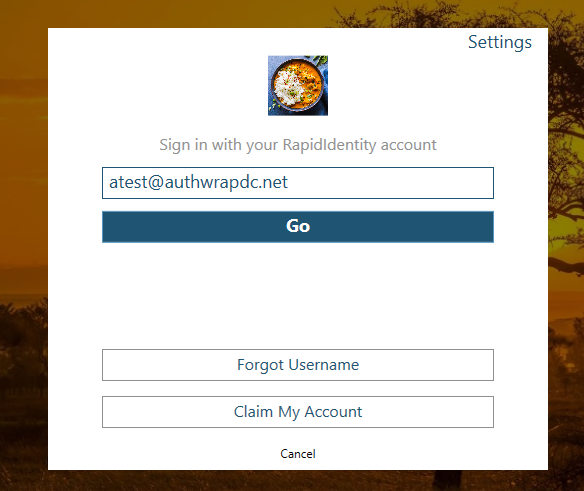
Step 2: Once the username is verified we will see all the Authentication Policies list which was assigned by the Admin on RI for user(s).
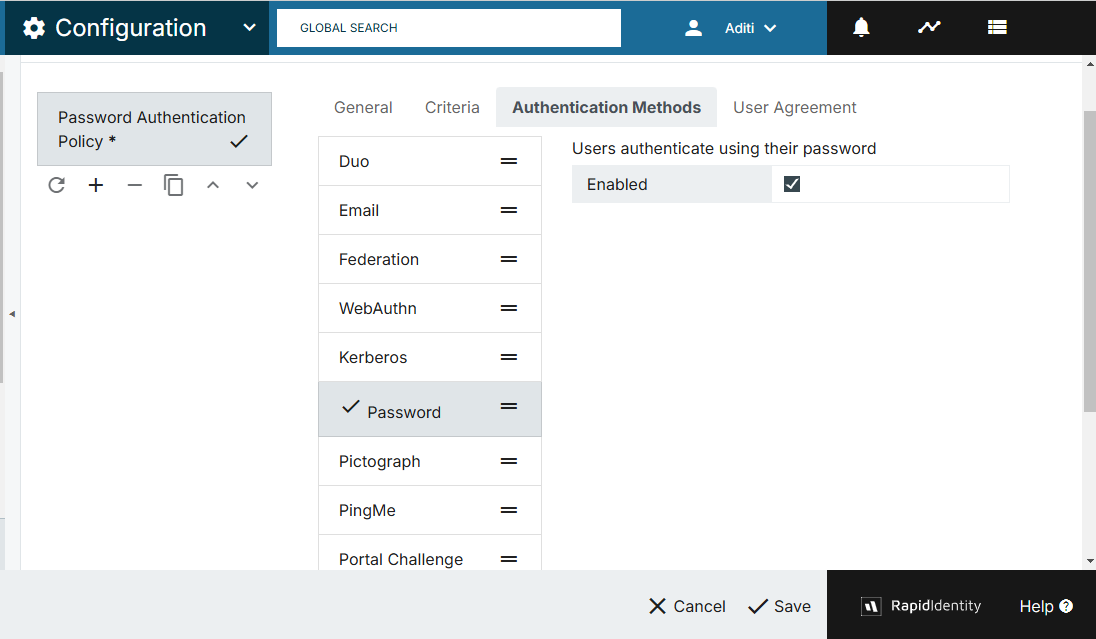
Step 3: User Select any method for login (All methods WAC support).
Step 4: User Credentials verification at RI level and AD level.
Step 4: When user Enter Password the Password will be initially verified using BE existing API then secondly verify the Domain, User email and Password with AD Server and Authenticate user in Windows Machine. If user credentials will fail it’s verification at any stage then we will give an error message to user.
Demo Video for Reference