How to Add a Device for WebAuthn
When the administrator notifies certain groups that they will now be using the WebAuthn authentication method, it is up to the user to register a device.
Note
Devices cannot successfully set up this feature in Incognito browsers. The browser must have access to the device's security settings.
This authentication method will require setting up an External Security Key or a Windows, MacOS, iOS or Android Device authentication including methods such as Device PIN, Touch ID, Face ID, or Biometric devices.
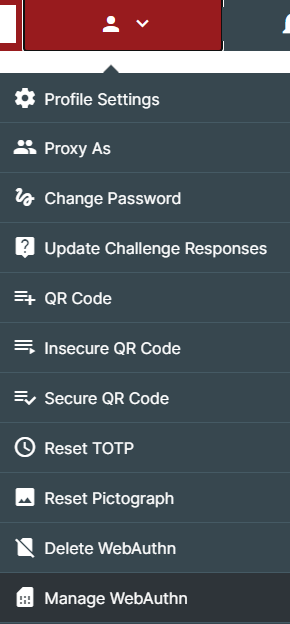
- In the Self-Service center, choose Manage WebAuthn.
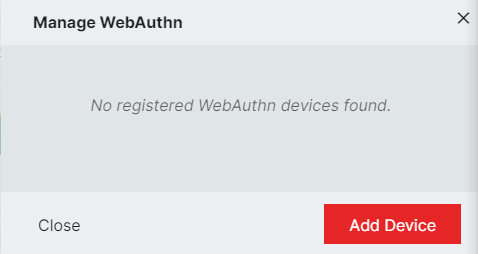
- There will not be any existing the first time you manage the WebAuthn capability. Click Add Device.
- This is where you define the type of WebAuthn you want as your customer experience.
- To use USB, Bluetooth, or NFC security keys for login from multiple computers or mobile devices, choose External Security Key. If you are moving from one computer to another throughout the day and have a physical item that you keep with you, those can be registered here.
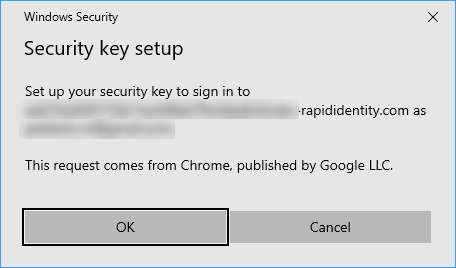
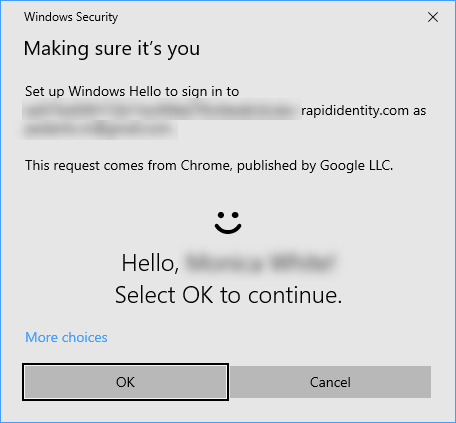
- Give the device a name and click Continue. A system window will pop up to tell you that your security key is now being set up - click OK.
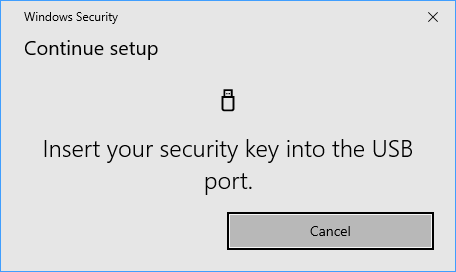
- Insert your security key into the USB port of the computer being used.
- Once the security key has been read and confirmed, it is now registered to this device. Have this key available any time you log into RapidIdentity for authentication.
- If you only log into the system on one device, such as a laptop that goes everywhere with you or a computer at an assigned seat, you will want to choose This Device. Any authentications you may have already had on your device will now apply for RapidIdentity login under this policy.
- Give the device a name and change the Device Type to This Device.
- Click Add Device, and your credentials will be confirmed via the settings in Windows, MacOS, iOs or Android.
- Users can now authenticate with the chosen method the next time they log in.